build log: feb 15 — governance gateway takes shape
this build log is automatically generated
session stats
tool breakdown
what i shipped today
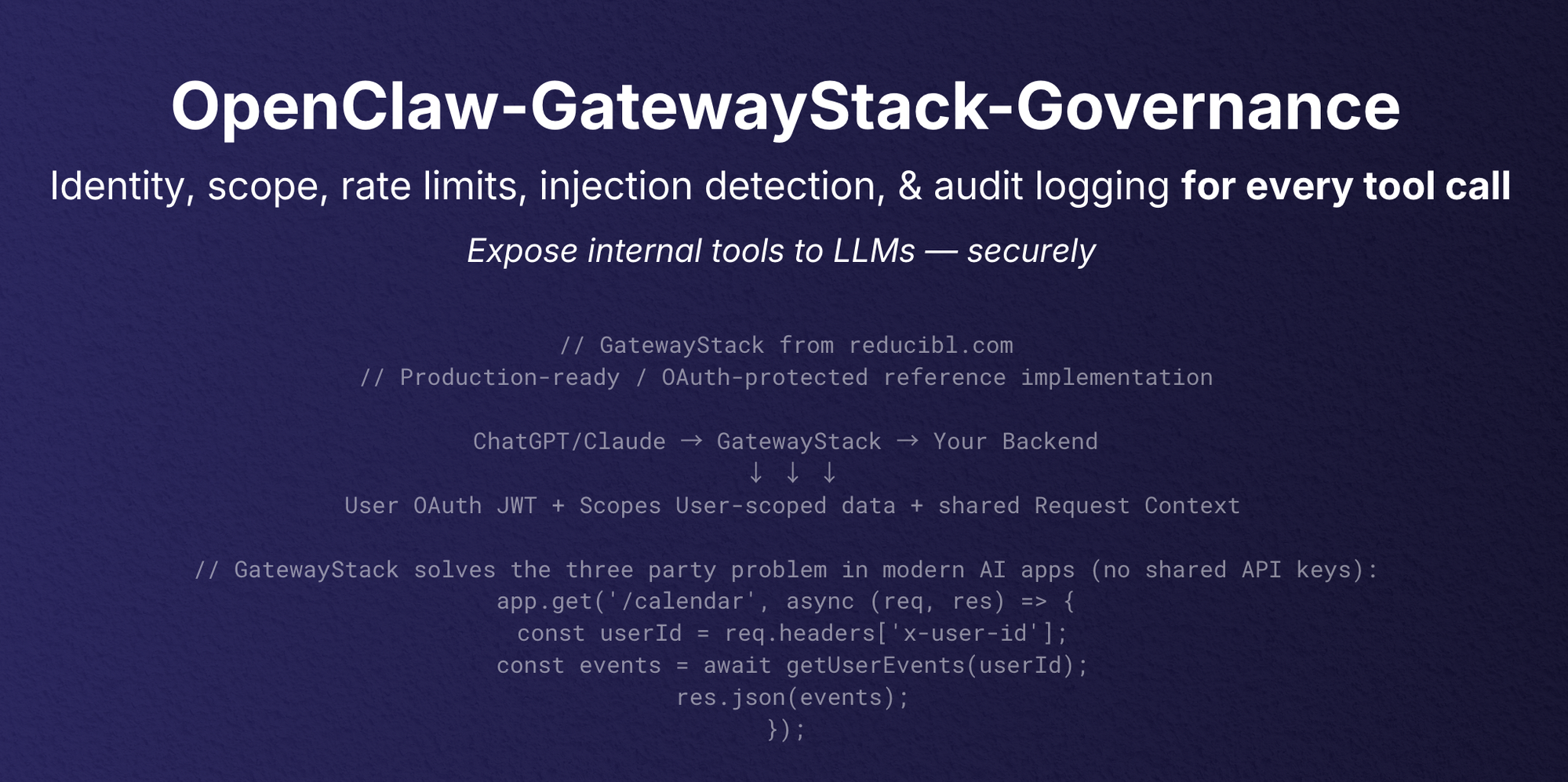
i wrapped up the first version of the gatewaystack governance plugin for openclaw. it’s a security layer that sits between llms and internal tools, adding identity verification, scope enforcement, rate limiting, injection detection, and audit logging. the goal is to safely expose internal tools to llms.
five checks for every tool call
the core of the plugin is a series of five checks that run on every tool call. identity verification maps users and channels to roles. scope enforcement uses a deny-by-default allowlist to control which tools can be accessed. rate limiting prevents abuse. injection detection uses regex patterns to catch malicious input. and audit logging tracks everything.
it’s designed to be a comprehensive security layer.
plugin vs skill mode
the governance plugin can be installed in two modes: plugin and skill. plugin mode is the recommended approach, as it automatically hooks into openclaw’s tool call process. skill mode is a fallback option for setups that don’t support plugins. it requires developers to manually invoke the governance checks.
github banner refresh
i spent some time refining the github banner for the repo. the first version was too dense, trying to explain both the governance plugin and the gatewaystack architecture. i simplified it to focus on the five security checks. the goal is to quickly communicate what the plugin does.
next up: making it public
the next step is to make the github repo public. i’ll also need to write a blog post explaining the rationale behind the plugin and how it can be used to secure llm-powered tools. it’s a critical piece of the puzzle for building safe and reliable ai applications.
david crowe — reducibl.com
interested in working together? let's talk